- Business Transformation
- cloud
- Cloud service Provider
September 4, 2023
The IT manager’s dilemma – security first or cloud first?
Data is central to everyone and everything
Many companies move to the cloud without fully considering the security implications. They may think a little about security, but when shifting operations to the cloud, it might not always get the attention it should: your cybersecurity approach and systems need to transform alongside your overall IT transformation and strategy.
Today, organizations are home to vast piles of data, generated by an ever-growing number of connected devices and systems. And along with this massive growth in data naturally comes an increased risk of data breaches.
To help address this, there is a growing number of security-related regulatory compliance initiatives. These include the EU’s Generation Data Protection Regulation (GDPR) and Gaia-X, a federation of European data infrastructure and service providers. Other schemes include the Payment Card Industry Data Security Standard (PCI DSS). You must remain continuously well informed about updates and modifications to any of these regulations to stay compliant and keep data secure.
Using a responsibility assignment matrix (RACI) can be worthwhile to ensure clarity and help achieve your end goals. RACI represents “responsible, accountable, consulted and informed,” and it is an approach that can help the cloud provider and the customer to understand each other’s responsibilities and needs. No cloud vendor will be able to cover every angle from the beginning of an engagement, so organizations should take control and ask their cloud vendor the right questions. Those questions should cover crucial areas of focus such as:
- Privileged access
- Backup and recovery
- Patching and updates
- Constant monitoring
- SIEM solutions
- NOC / SOC
- Regulatory compliance
- Long-term viability
- Data location
- Investigation status
- Data segregation
- Availability
Circumstances determine the approach
Pre-COVID, you or your service provider’s IT managers typically had a clear plan and roadmap of how to transform the IT environment, what to do and when. There was a value in joint opportunity assessments and establishing the speed of change for your organization. I have seen businesses driving their IT strategy based on their business roadmap, where IT budgets were also established based on business demand or throughput. I call this phase the IT blueprinting phase.
During COVID, the speed at which transformation could take place changed, with IT service design and strategy linked to employees working from home and changes in customer expectations. Joint opportunity assessments had to be conducted virtually due to lockdowns, meaning no face-to-face meetings. So, while the speed at which IT transformed was very fast, there was a shift from business leading IT to IT enabling business. IT budgets, which used to be allocated over five years, were brought forward as customers couldn’t operate within the time, agility and speed of market that COVID created. I refer to this situation as COVID transformation rather than digital transformation. During this time, we also saw an acceleration in thinking around zero-touch management through extreme automation, cloud-ready infrastructures, resilient network and enhanced cybersecurity.
It meant companies did not have sufficient time to evaluate how a change in IT design or strategy would link to their overall IT blueprint with respect to the introduction of new SaaS or infrastructure moving from on-premises to cloud. Furthermore, companies did not have time to review the overall security posture. I call this phase “push-push,” rather than it being a time of companies implementing thinking based on a clear IT roadmap or blueprint.
Post-COVID, there will be a shift towards a hybrid model, both in how IT facilitates future architecture and how business and IT will co-exist, with defined objectives meeting organizational goals. IT will need to focus on two important factors: first, cloud computing has evolved and has fast become even more flexible and reliable; and second, the massive influx of thousands of small-scale enterprises into the digital space, companies that had previously not been part of the equation.
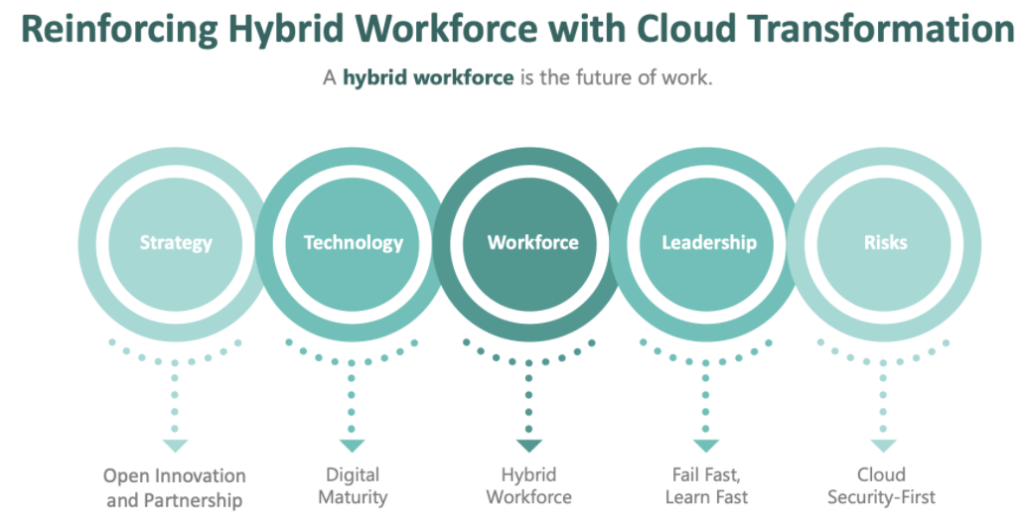 (Image source: www.itconductor.com)
(Image source: www.itconductor.com)
In summary: security first, cloud or no cloud
Security must simply be built into your thinking from the start of your conversations with a cloud provider. Some organizations can worry about putting vital business functions such as IT or payment systems into the cloud because of security concerns. Still, it is important to remember that the challenge is not in the security of the cloud itself.
In most cases, data breaches are usually a result of user error, not the cloud provider failing to enforce proper security policies and controls. If you implement robust security policies built on zero-trust principles and train your employees to follow those principles correctly, you should have a safe, secure cloud journey.